What Is SAST vs DAST for AI-Built Apps?
 Mr. Ballaz
Mr. Ballaz- Focus
- SAST vs DAST
- Risk
- High
- Stack
- Supabase/Next.js
- Detection
- Ubserve Runtime Simulation

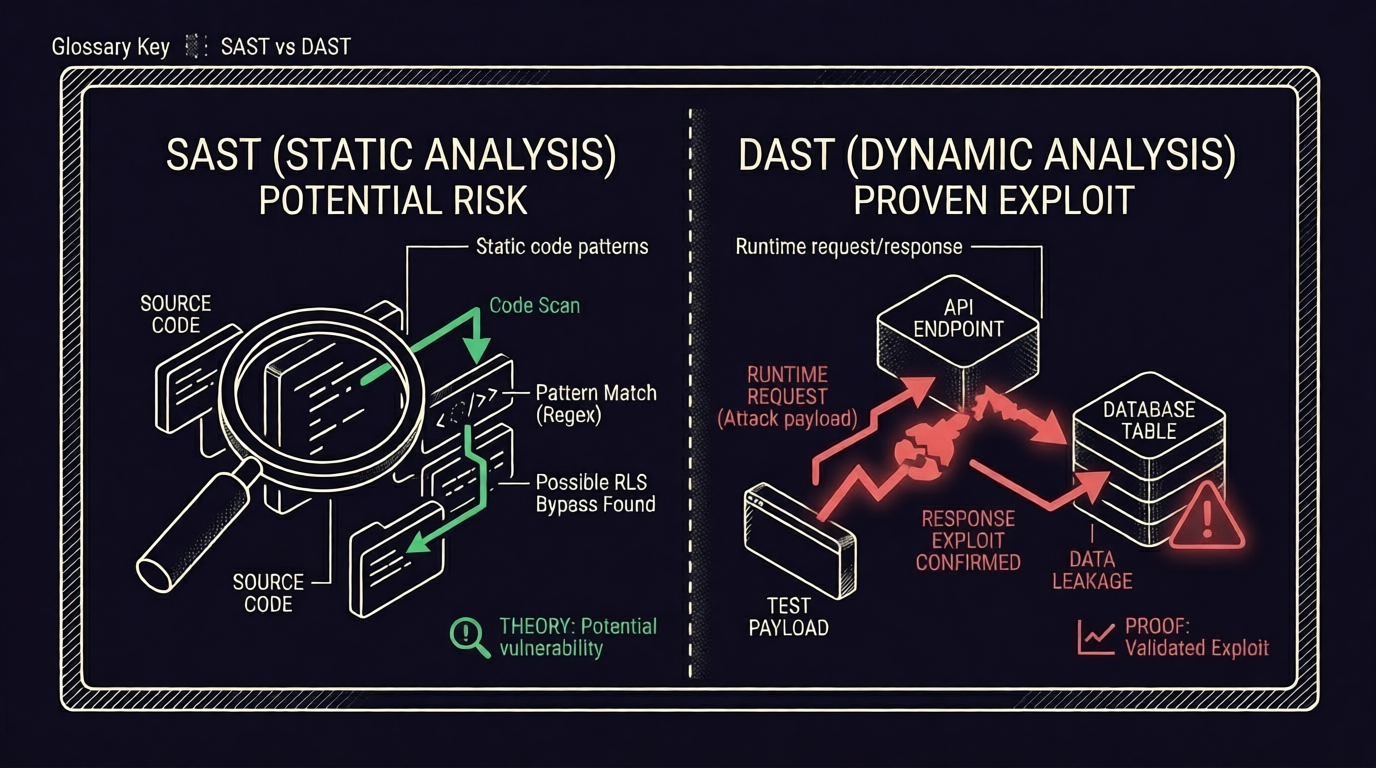
SAST vs DAST is a security testing comparison that separates code analysis from live exploit validation. AI-built apps usually need both to catch logic and runtime gaps.
SAST identifies potential insecure patterns in code; DAST validates exploitability in running application behavior.
SAST analyzes source code for insecure patterns without executing it. DAST tests a running app to confirm whether an attacker can exploit behavior in production-like conditions.
For AI-built apps, this distinction matters more because generated code often looks structurally correct while still failing business-logic authorization paths at runtime. Founders should treat SAST as early signal and DAST/runtime testing as release proof.
A non-technical analogy: SAST is proofreading a script for mistakes, while DAST is performing the play on stage to see where the scene actually breaks in front of an audience.
Start free scan | See sample audit
Agentic Risk (Cursor, v0, Bolt)
In AI-built stacks, generated logic often passes static checks while failing runtime authorization boundaries. Ubserve 2026 data indicates 2.1x more launch-blocking findings were confirmed in runtime tests than in static-only triage.
Wrong vs. Right
WRONG: SAST-only release decision for AI-generated auth/data paths
RIGHT: SAST for breadth + DAST/runtime simulation for launch confidence
Copy-Paste Fix Prompt for Cursor/Claude
Create a combined SAST+DAST security workflow.
1. Keep static checks for dependency/code hygiene.
2. Add runtime exploit simulation for auth, billing, and tenant data routes.
3. Fail release if confirmed high-risk exploit paths remain.
4. Output CI steps and local verification scripts.
Return YAML + test commands.
Run your first scan free at ubserve.com.
Related resources
How Ubserve Applies This in Real Scans
Ubserve treats What Is SAST vs DAST for AI-Built Apps? as a production risk, not a theory term. Our runtime simulation maps this control to attacker paths in auth, data access, and API behavior, then returns fix-ready guidance tied to your stack. OWASP-style principles are used as the baseline, but we prioritize what is actually exploitable in your live flow.
Runtime exploit simulation + behavioral authorization checks.
Clear proof path showing where trust boundaries fail.
AI-ready fix prompts and implementation-level patch guidance.
FAQs
Should founders choose SAST or DAST?+
Want Ubserve to test this risk in your app?
Run a scan and get attacker-first validation, exploit evidence, and fix guidance mapped to what is sast vs dast for ai-built apps?.